Control Your
Patient Data
Wherever it Goes
Seald Healthcare gives you full control over your patient data by encrypting PHI at the source. Set, enforce, and revoke access in real time, even after data is shared, without disrupting workflows.
NEW RESOURCE
Compliance vs. Security in Healthcare
Since 2009, over 846 million patient records exposed, with the average breach costing $9.77 million. This white paper examines why HIPAA compliance alone cannot prevent breaches and how a data-layer security approach closes the gap.
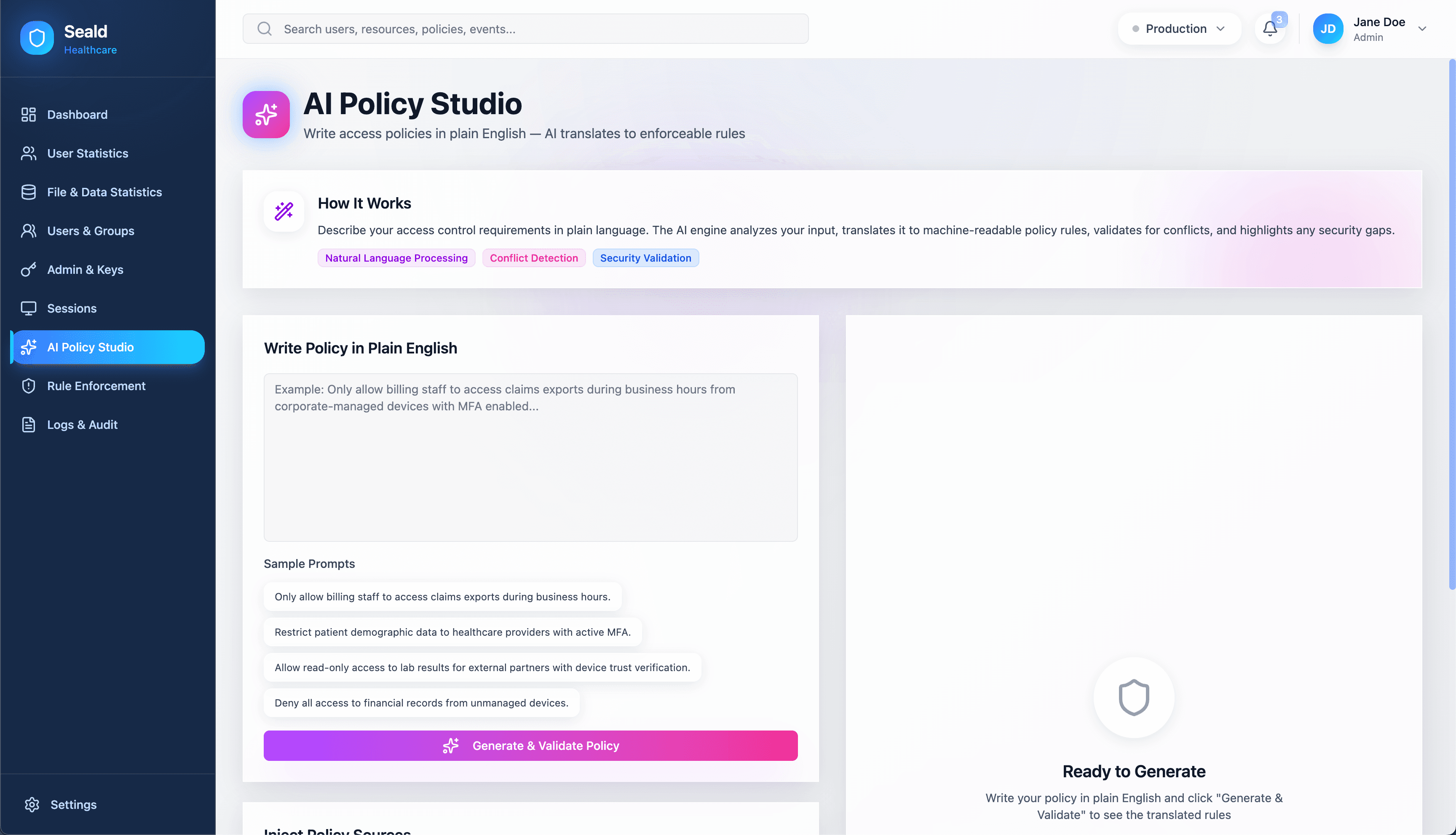
Write Access Policies in Plain English
with our AI Policy Studio
Define and enforce access policies in plain English. Seald Healthcare's AI Policy Studio translates natural language into cryptographically enforced rules that travel with the data, so administrators can write policies like “Only allow clinical staff to decrypt patient records during office hours” without configuring complex rule engines.
Our Mission
Seald Healthcare's mission is to ensure that every piece of patient data is protected and under the organization's control, not just where it is stored, but wherever it travels. We combine deep expertise in applied cryptography, healthcare compliance, and enterprise software to close the industry's most fundamental security gap. Protecting patient data should never come at the cost of clinical efficiency.
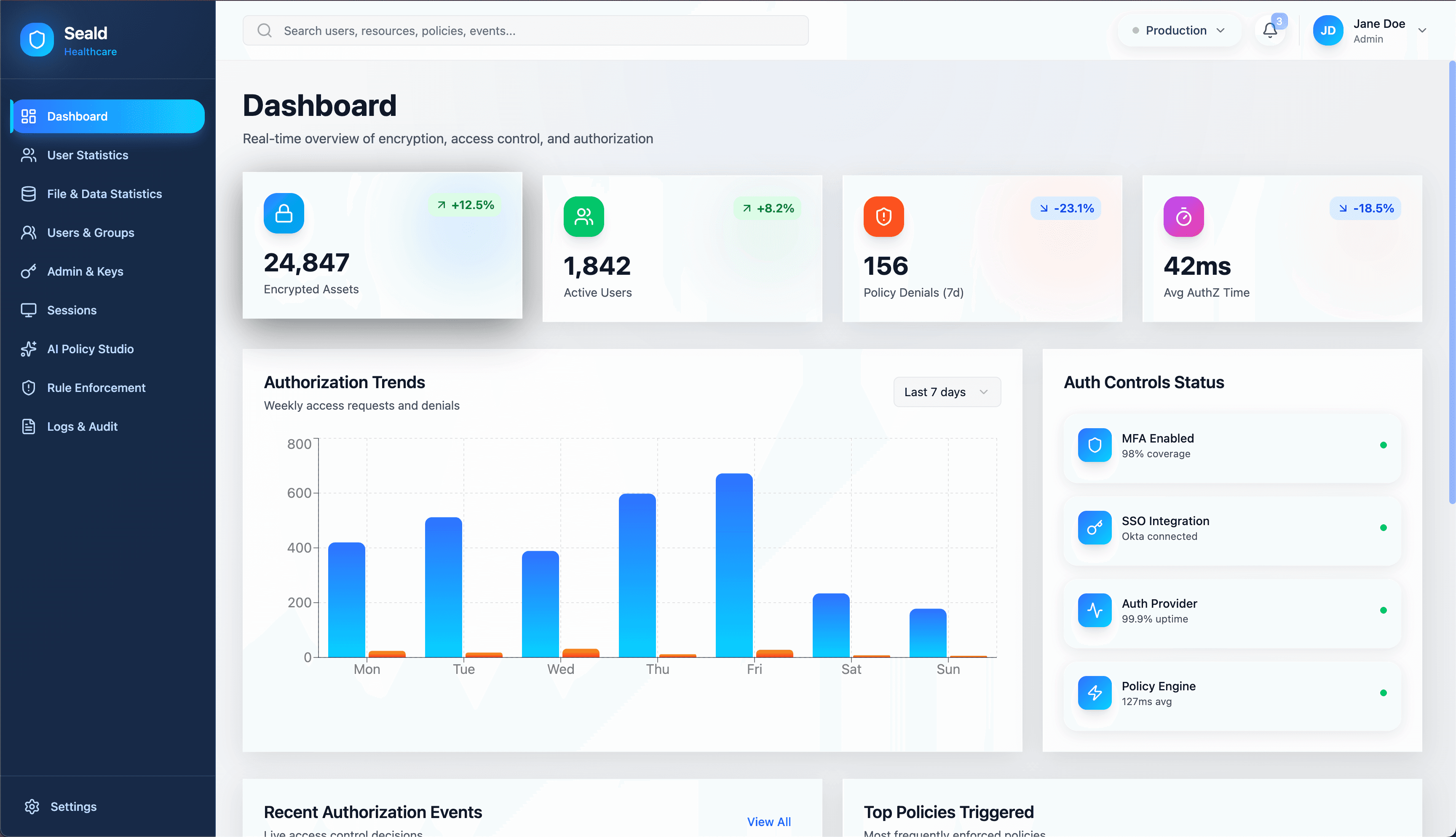
See it in Action
A simple, intuitive interface for managing encryption, access policies, and audit logs across all your healthcare workflows.
How it Works
Seald Healthcare integrates seamlessly so your team can focus on delivering high-quality care while keeping patient data secure.
Integrate
Add the Seald Healthcare SDK to your applications or workflows. Works with EHRs, portals, messaging, file sharing, and custom apps, and complements AWS, Google Cloud, and Azure environments.
Encrypt and Set Policy
Data is encrypted at the source before it leaves your system. Access policies travel with the data, not the network.
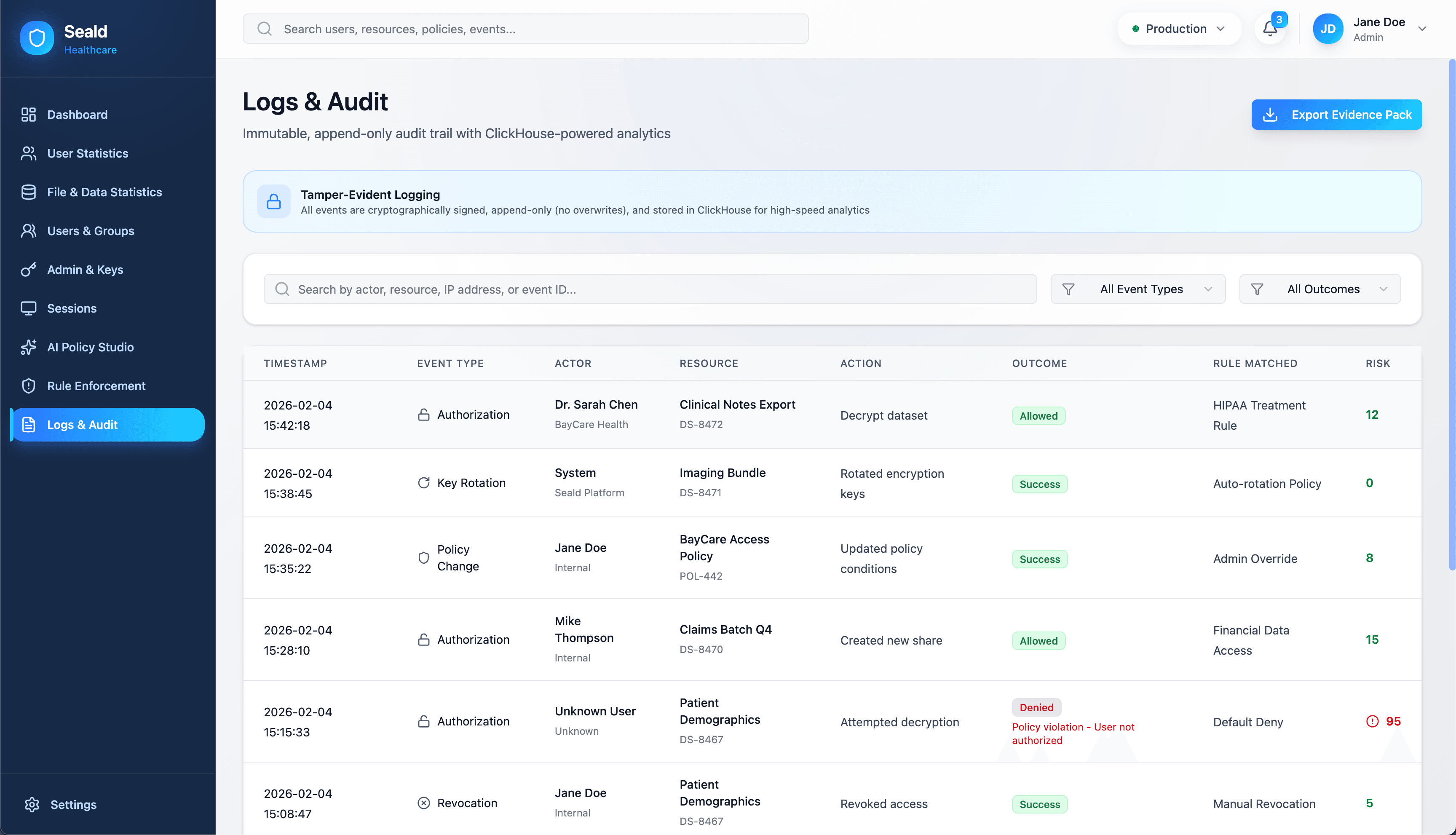
Control After Sharing
Revoke access, update permissions, and audit usage in real time. Policies are enforced at decryption, not at the perimeter.
Ready to Be Secure — Not Just Compliant?
Seamlessly encrypt and remove plaintext PHI. No rip-and-replace required.